Intro To 'sha224sum' Command In Linux
2023-08-16 - By Robert Elder
I use the 'sha224sum' command to compute the SHA 224 checksum of a file or stream:
sha224sum file1.txt
4575bb4ec129df6380cedde6d71217fe0536f8ffc4e18bca530a7a1b file1.txt
About SHA 224
SHA 224 is one of 4 message digest algorithms that are part of the SHA 2 family that was created to replace the SHA 1 message digest algorithm.
The SHA 224 message digest has the smallest output size of all SHA 2 family hash functions that are listed in 2008 revision of the FIPS 180 standard:
sha224sum file1.txt
sha256sum file1.txt
sha384sum file1.txt
sha512sum file1.txt
4575bb4ec129df6380cedde6d71217fe0536f8ffc4e18bca530a7a1b file1.txt
7f83b1657ff1fc53b92dc18148a1d65dfc2d4b1fa3d677284addd200126d9069 file1.txt
bfd76c0ebbd006fee583410547c1887b0292be76d582d96c242d2a792723e3fd6fd061f9d5cfd13b8f961358e6adba4a file1.txt
861844d6704e8573fec34d967e20bcfef3d424cf48be04e6dc08f2bd58c729743371015ead891cc3cf1c9d34b49264b510751b1ff9e537937bc46b5d6ff4ecc8 file1.txt
What Is 'SHA224' Useful For?
According to section 6, 'SECURE HASH ALGORITHMS', of the documentation fips180-3_final.pdf:
In the following sections, the hash algorithms are not described in ascending order of size. SHA256 is described before SHA-224 because the specification for SHA-224 is identical to SHA256, except that different initial hash values are used, and the final hash value is truncated to 224 bits for SHA-224. The same is true for SHA-512 and SHA-384, except that the final hash value is truncated to 384 bits for SHA-384.
This truncation of the output bits could make SHA 224 more suitable than SHA 256 for applications with extremely limited storage space. The SHA256 hash function has an output size of 256 bits, while the output size of SHA1 is 160 bits. Since the primary purpose of SHA256 was to replace the older SHA1 hash function, one could speculate that there was a desire for existing applications to be able to 'upgrade' to a newer hash function that was still more secure than SHA1, but didn't require as much storage space as SHA256. SHA224 could therefore satisfy this requirement by only requiring 64 additional bits of storage instead of the 96 that were required if upgrading to SHA256.
Another potential purpose of SHA224 would be to act as a fallback if a fatal cryptographic vulnerability was ever discovered in the initial values used by SHA256. The SHA256 hash function initial values come from "taking the first thirty-two bits of the fractional parts of the square roots of the first eight prime numbers.", and for SHA224, they come from the second set of 32 bits of "the first sixty-four bits of the fractional parts of the square roots of the ninth through sixteenth prime numbers." (as you can see by inspection from the list of initial values for SHA384).
Other Standard Features Of 'sha224sum'
The 'sha224sum' command supports all of the same flags and features as the sha256sum command, such as reading input from stdin:
echo -n "Hello World!" | sha224sum
4575bb4ec129df6380cedde6d71217fe0536f8ffc4e18bca530a7a1b -
or verifying checksums in a file, just like the 'sha224-checksums.txt' file shown below:
4575bb4ec129df6380cedde6d71217fe0536f8ffc4e18bca530a7a1b file1.txt
0808f64e60d58979fcb676c96ec938270dea42445aeefcd3a4e6f8db file2.txt
0a2bc52e62761d814bffe5a76dc9806a91bccbe634563c66ebfbe702 file3.txt
sha224sum -c sha224-checksums.txt
file1.txt: OK
file2.txt: OK
file3.txt: OK
And that's why the 'sha224sum' command is my favourite Linux command.
 Intro To 'stty' Command In Linux
Published 2023-10-04 |
 Buy Now -> |
 Intro To 'nproc' Command In Linux
Published 2023-07-15 |
 Intro To 'comm' Command In Linux
Published 2023-09-06 |
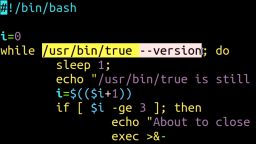 How To Force The 'true' Command To Return 'false'
Published 2023-07-09 |
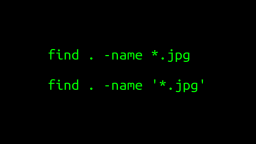 A Surprisingly Common Mistake Involving Wildcards & The Find Command
Published 2020-01-21 |
 A Guide to Recording 660FPS Video On A $6 Raspberry Pi Camera
Published 2019-08-01 |
 Intro To 'chroot' Command In Linux
Published 2023-06-23 |
| Join My Mailing List Privacy Policy |
Why Bother Subscribing?
|